Effective Tips to Protect Your iPhone Against Theft and Boost Security
In an era where our smartphones serve as an extension of our lives, the security of our devices is paramount. For iPhone users, safeguarding your device against theft is not just about protecting a piece of technology; it's about securing your personal information, memories, and ensuring uninterrupted connectivity.
This comprehensive guide is designed to empower you with effective tips to fortify your iPhone's defenses and enhance overall security. From practical measures to advanced settings, we'll explore the full spectrum of strategies to keep your iPhone safe.
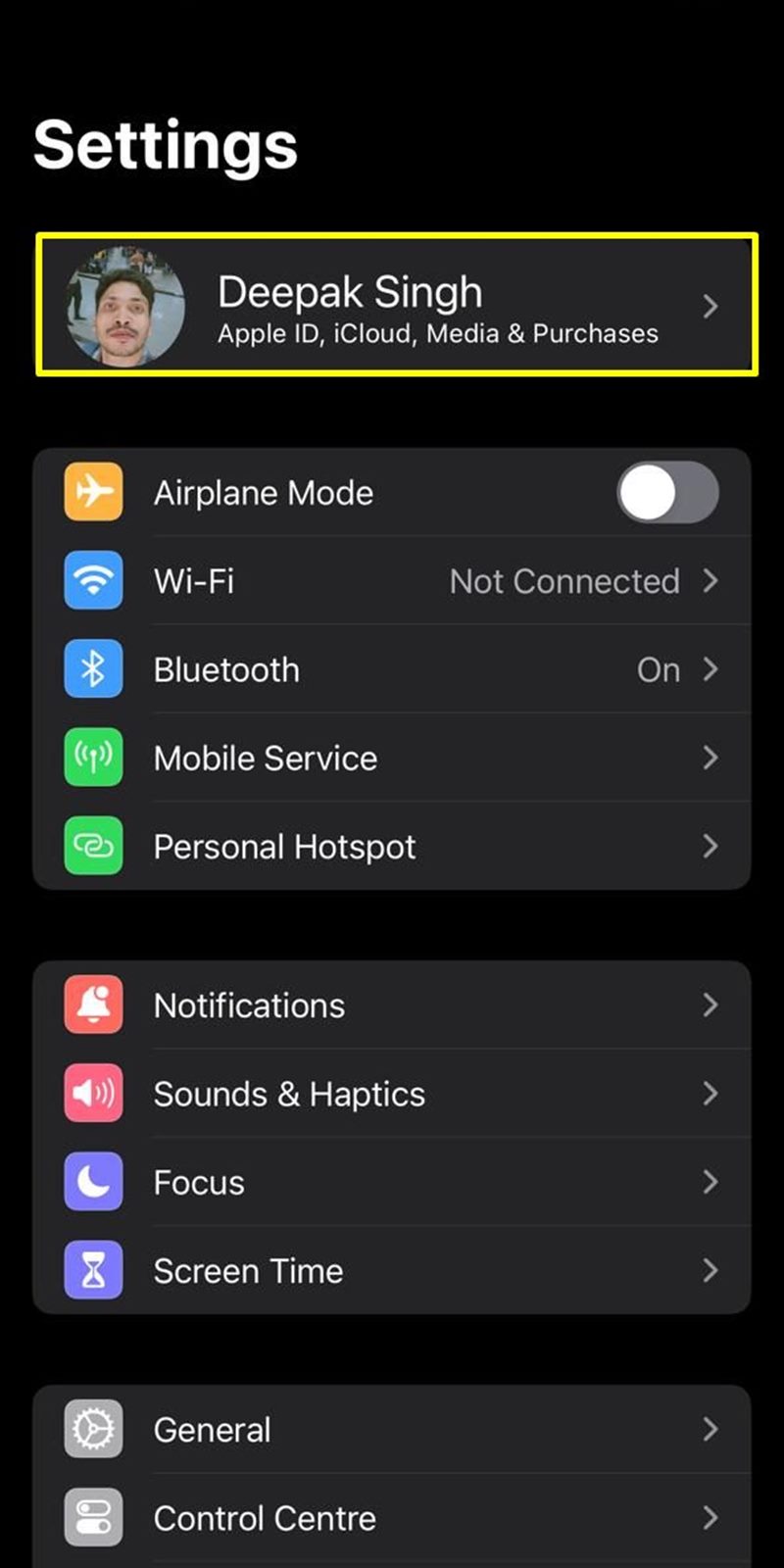
1. Activate Find My iPhone: A Powerful Anti-Theft Measure
One of the first lines of defense is to enable the "Find My iPhone" feature. This built-in tool not only helps you locate your device if it's lost but also allows you to remotely lock or erase its contents, rendering it useless to potential thieves.
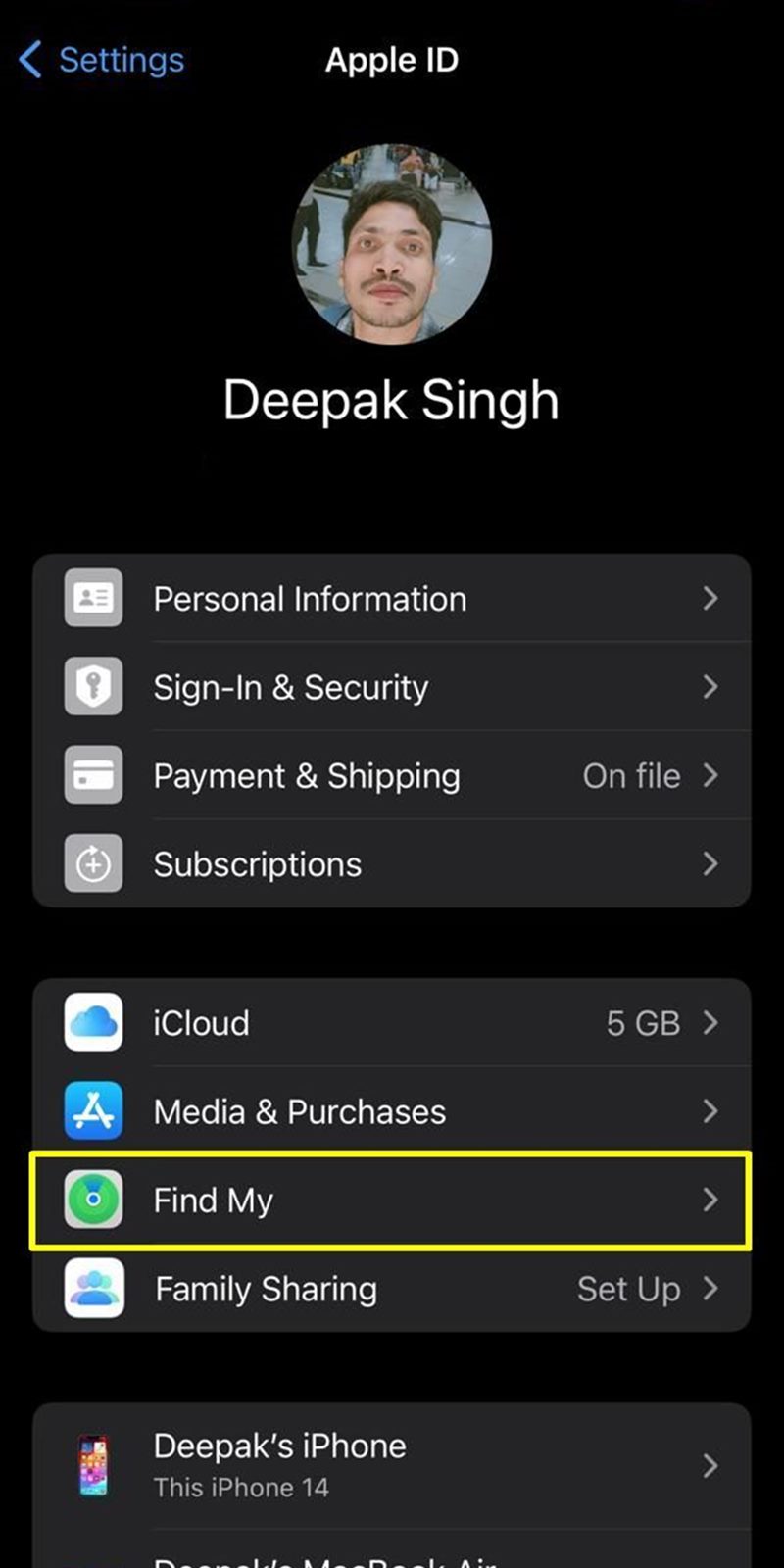
Here is how to activate "Find My iPhone"
- Go to Settings.
- Tap on your Apple ID.
- Select "Find My."
- Toggle on "Find My iPhone," "Find My Network," and "Send Last Location."
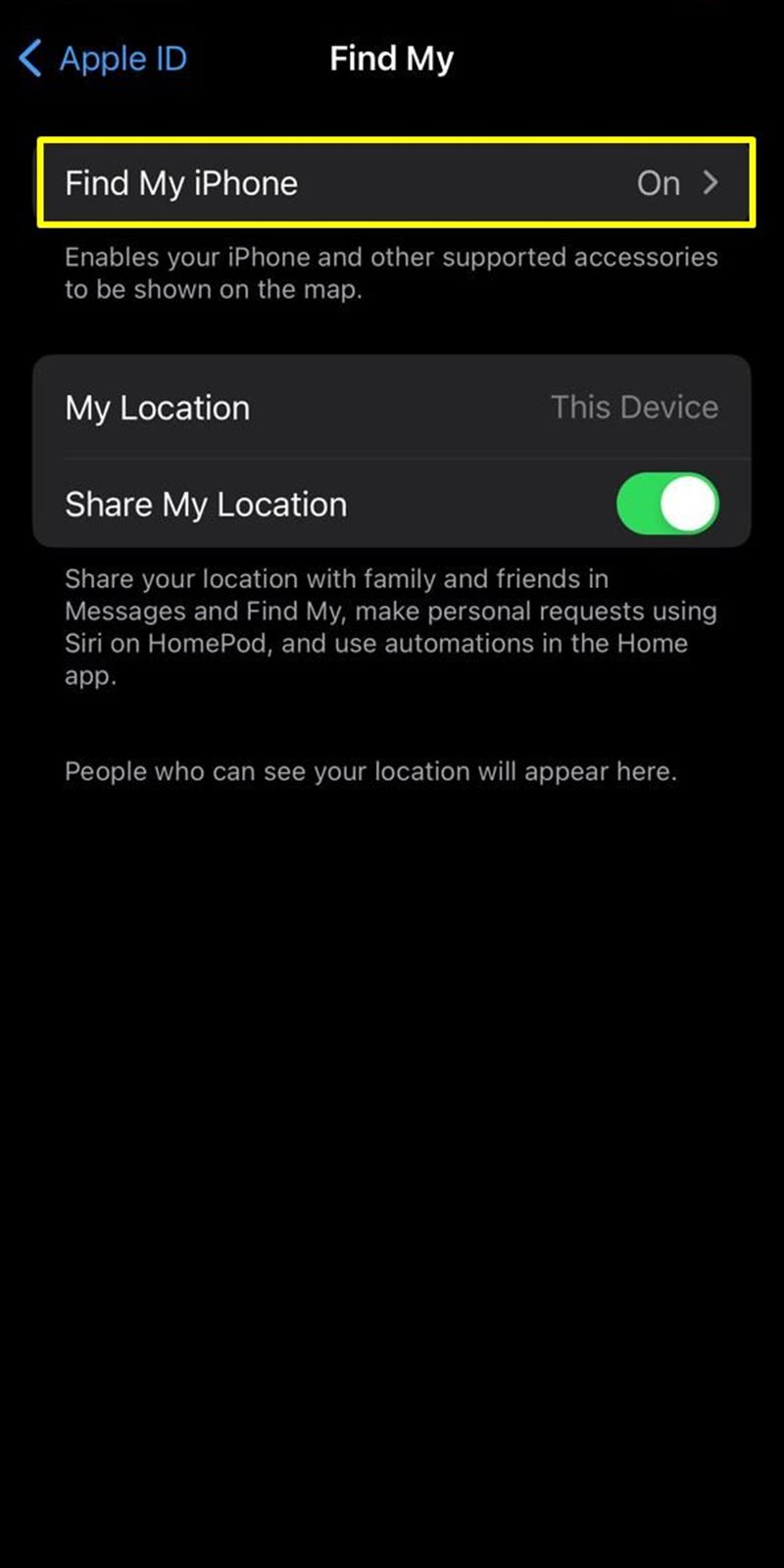
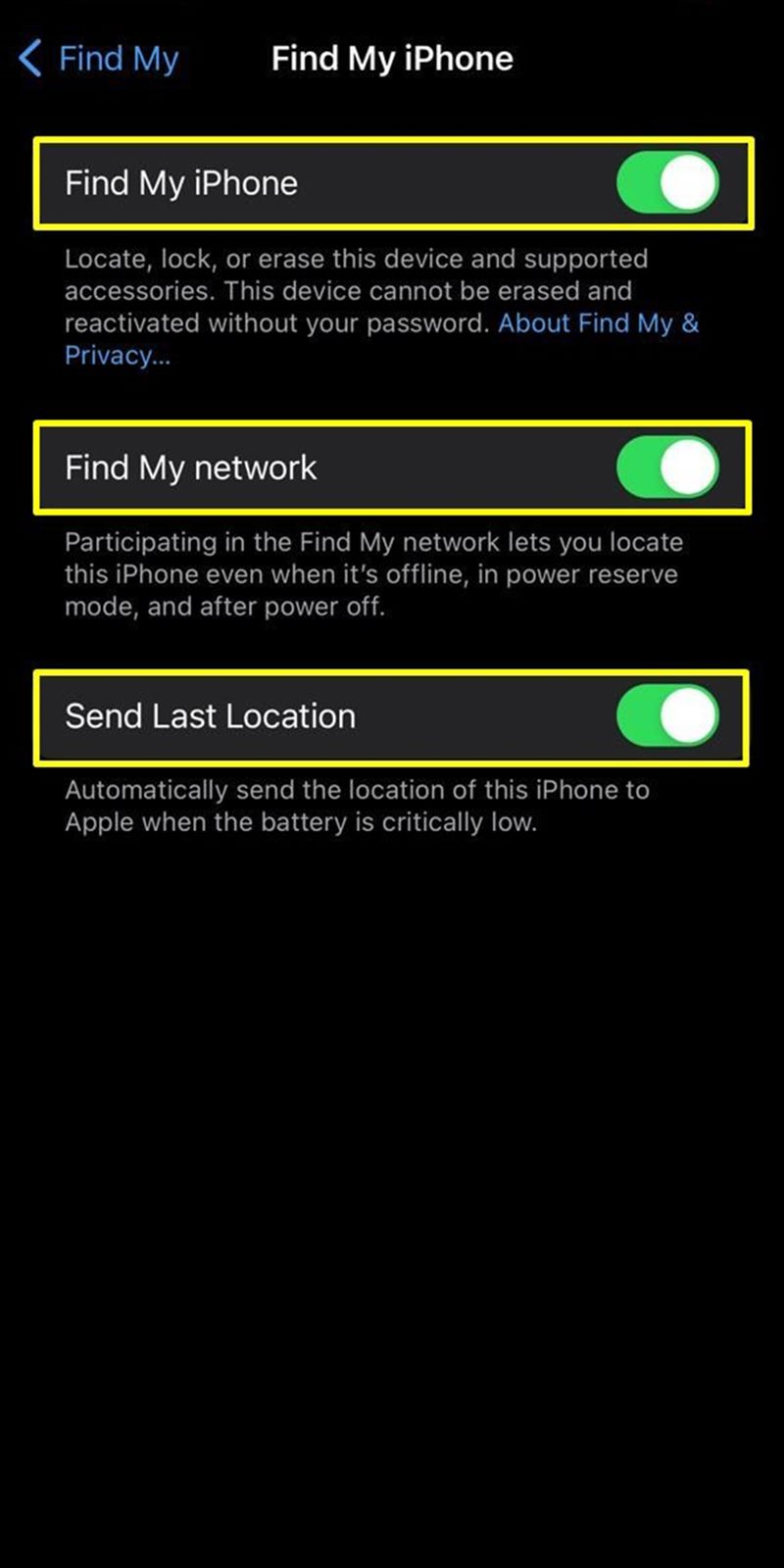
Find My iPhone
"Find My iPhone" is a security feature that helps you locate your lost or stolen iPhone. Once activated, you can use another Apple device or the iCloud website to track the location of your iPhone on a map.
Find My Networ
"Find My Network" is an extension of Find My iPhone and is part of Apple's broader Find My network. It leverages the Bluetooth signals of nearby Apple devices to anonymously and securely communicate the location of your lost device to iCloud, even if it's offline.
Devices in the Find My network, including those owned by other users, help locate your lost device by anonymously relaying its location information.
Send Last Location
Send Last Location is an additional feature within Find My iPhone that helps you track your device's last known location before its battery dies.
When your iPhone's battery is critically low, it automatically sends its last known location to Apple's servers. This information can be crucial in determining where your device was when the battery was about to die.
If your device runs out of battery and goes offline, you can still check the last location where it was operational. This feature aids in retracing steps and narrowing down the search area.
2. Disabling "Control Centre" and "Accessories" on iPhone Lock Screen
2. Disabling "Control Centre" and "Accessories" on iPhone Lock Screen In our increasingly digital world, ensuring the security of personal devices is paramount. Disabling certain features on the iPhone lock screen is a strategic move to prevent unauthorized access, safeguarding your privacy and protecting sensitive information. Disabling "Accessories" access from lockscreen prevent unauthorized access to connected accessories without unlocking the device.
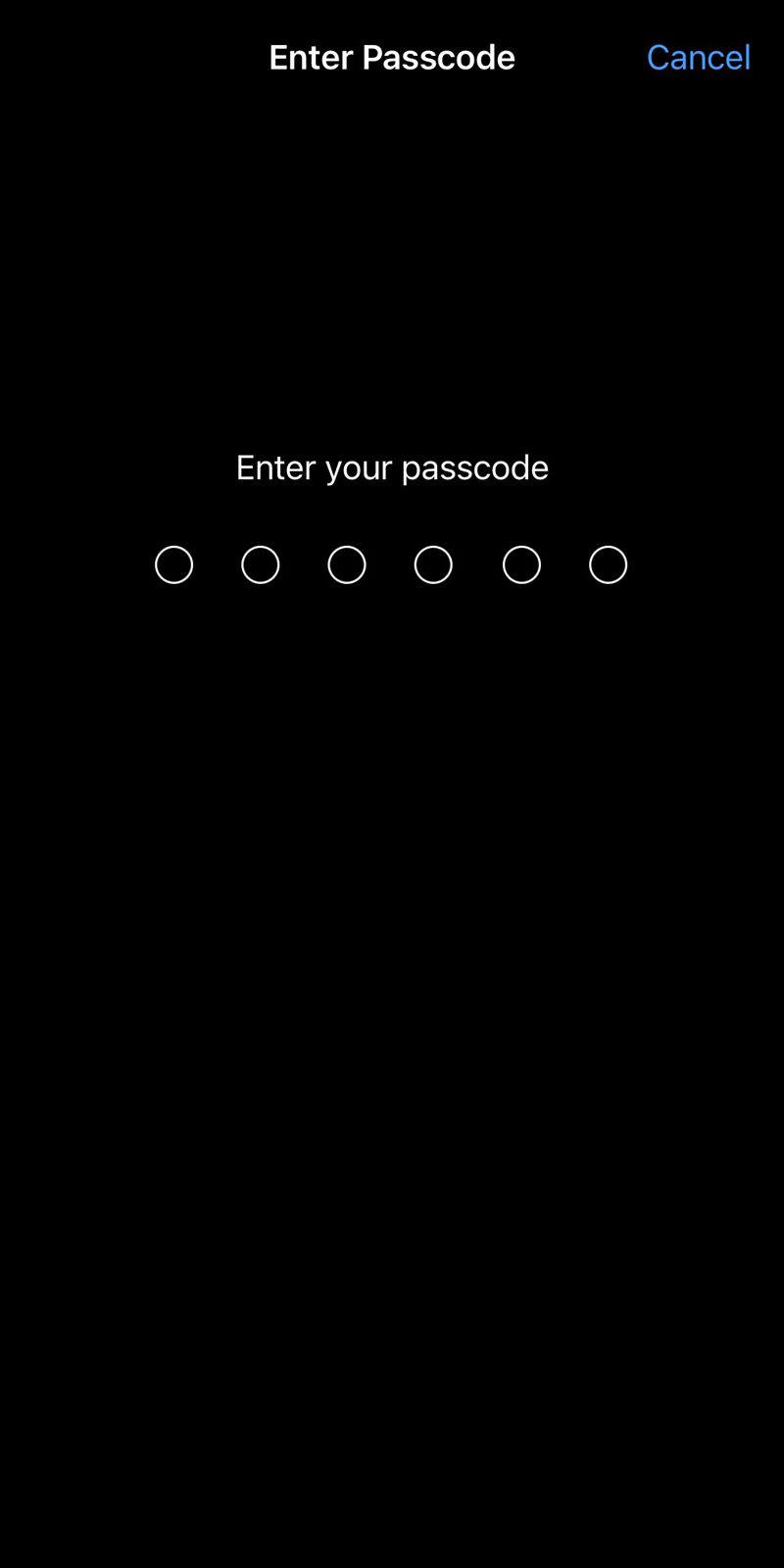
Here is how to disable "Control Centre" and "Accessories" on iPhone lock screen:
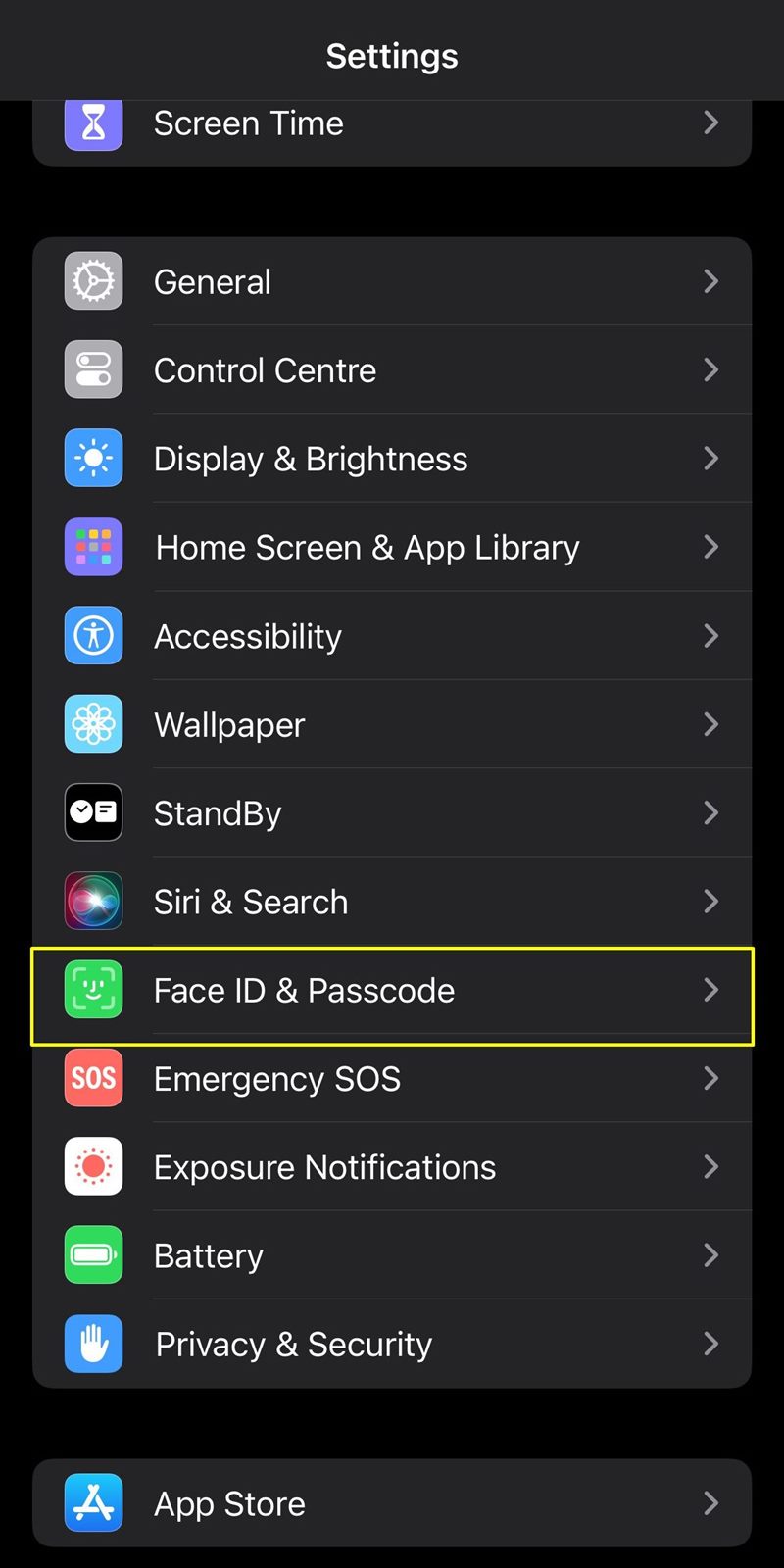
- Go to Settings.
- Tap on "Face ID & Passcode."
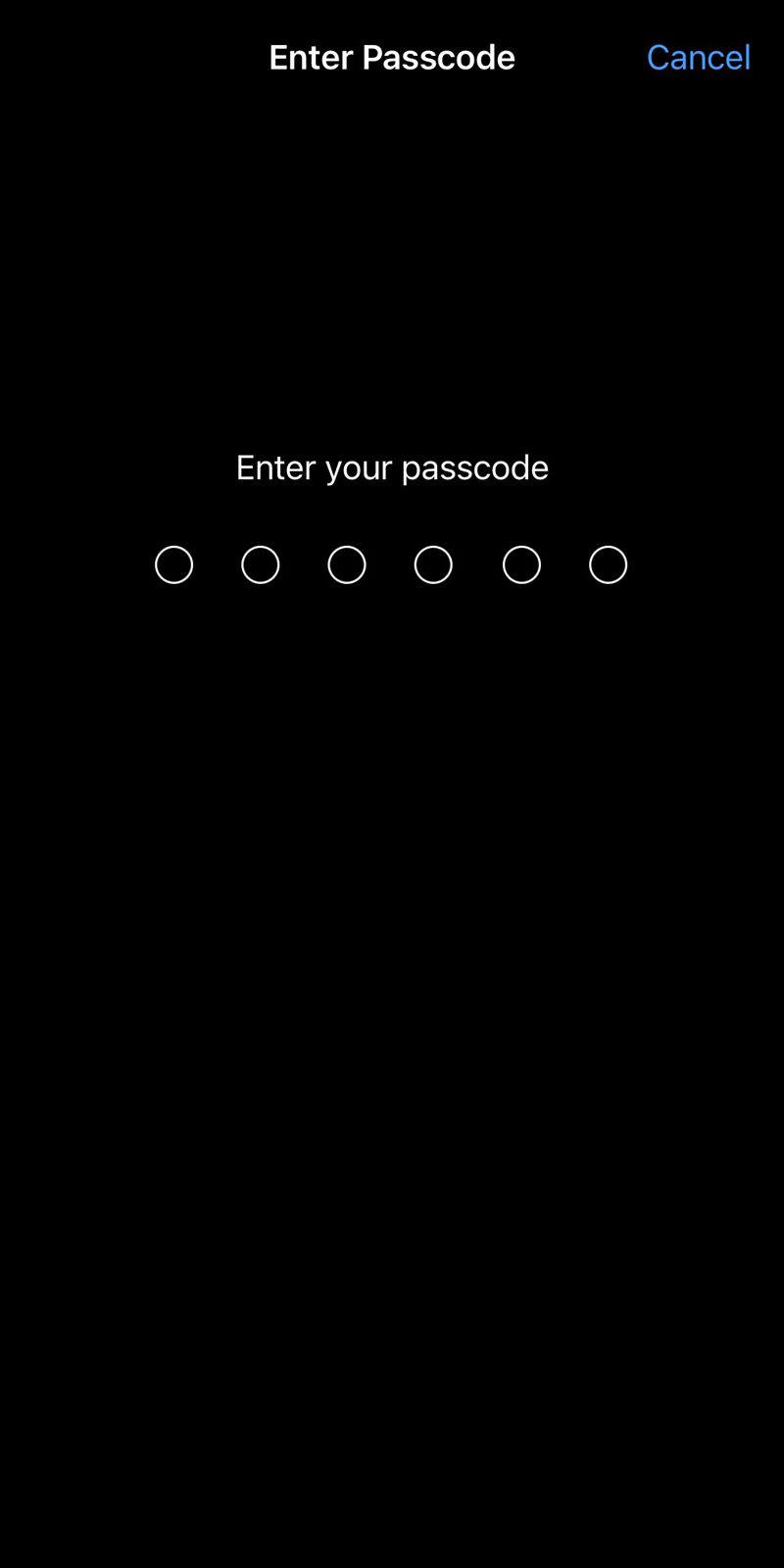
- Enter you passcode.
- Toggle on "Control Centre," "Wallet," and "Accessories."
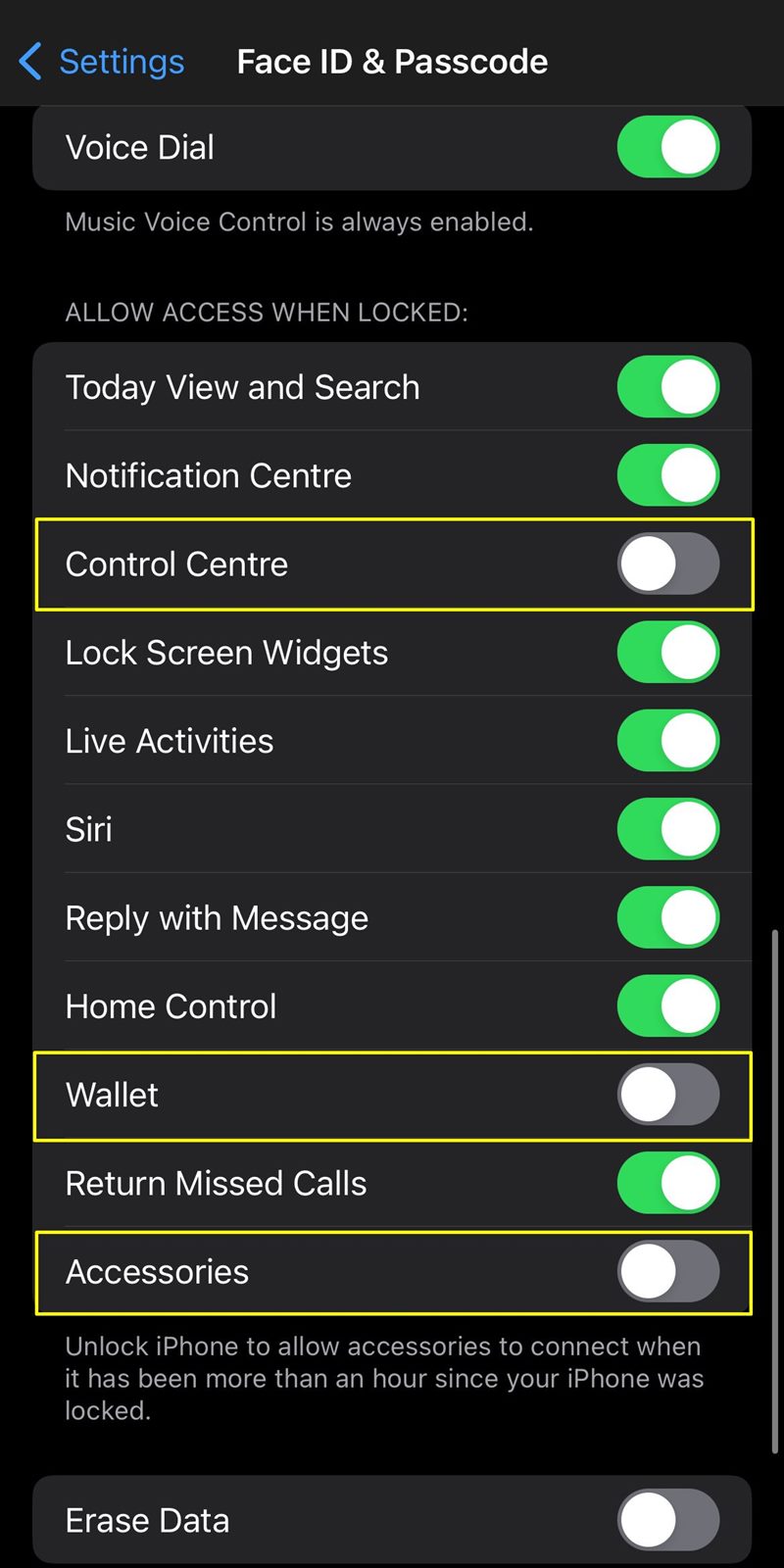
Control Centre
Disabling Control Center ensures that critical settings like Wi-Fi, Bluetooth, and airplane mode are not accessible without unlocking your iPhone. This adds an extra layer of privacy and prevents unauthorized changes.
Wallet
Disabling Wallet ensures that your financial and payment information remains secure. Without unlocking your iPhone, no one can access or make payments using your Apple Pay.
Accessories
Disabling USB Accessories ensures that connected devices cannot interact with your iPhone without authentication. This feature adds an extra layer of protection against potential data breaches.
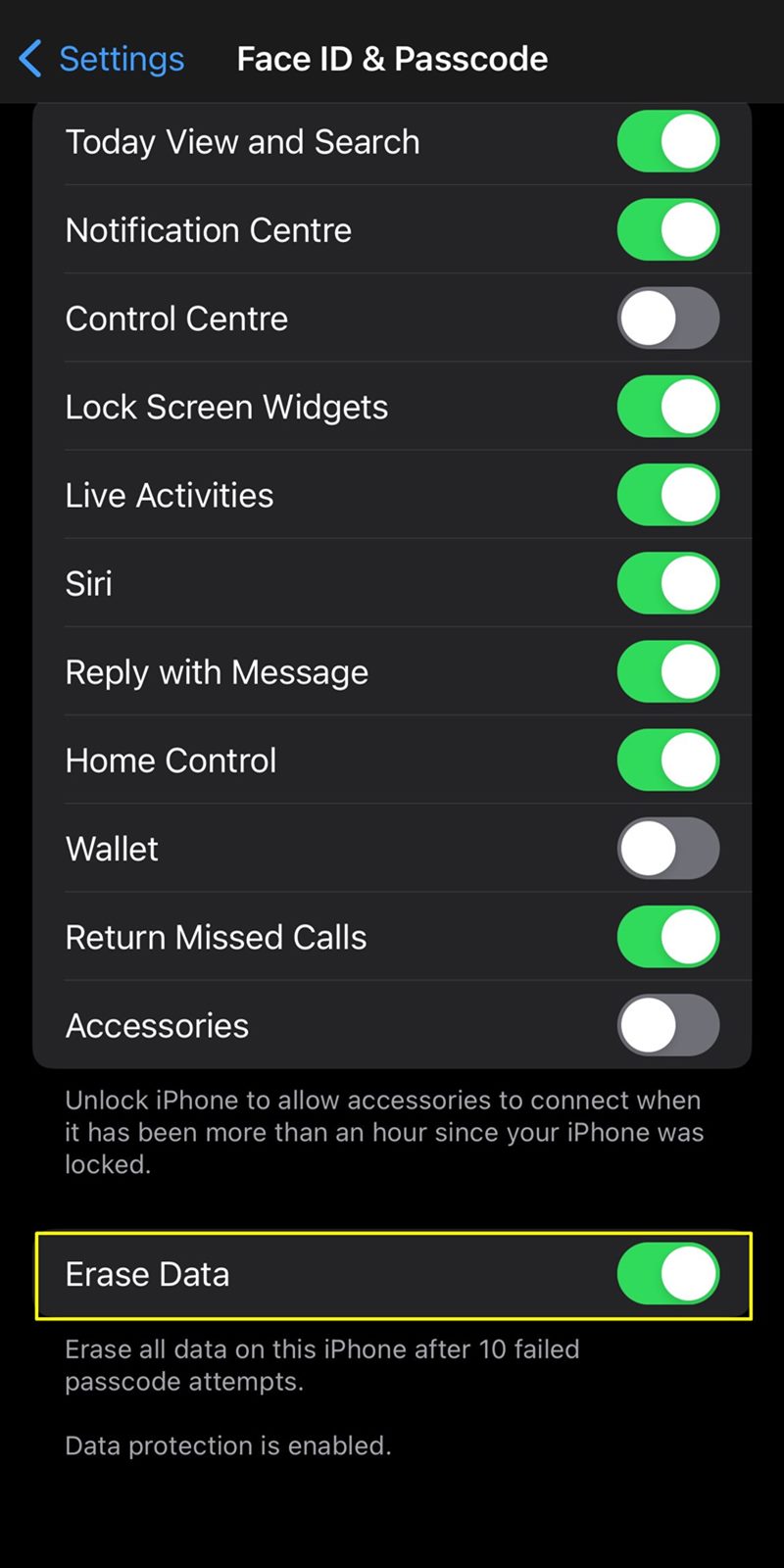
3. Activate "Erase Data": An Ultimate Measure for iPhone Security
In the realm of digital security, the "Erase Data" feature stands as a robust last line of defense against potential data breaches and unauthorized access. This setting, when activated, ensures that all data on your iPhone is permanently erased after ten failed attempts to unlock the device.
Here is how to activate "Erase Data":
- Go to Settings.
- Tap on "Face ID & Passcode."
- Enter your passcode.
- Toggle on "Erase Data."
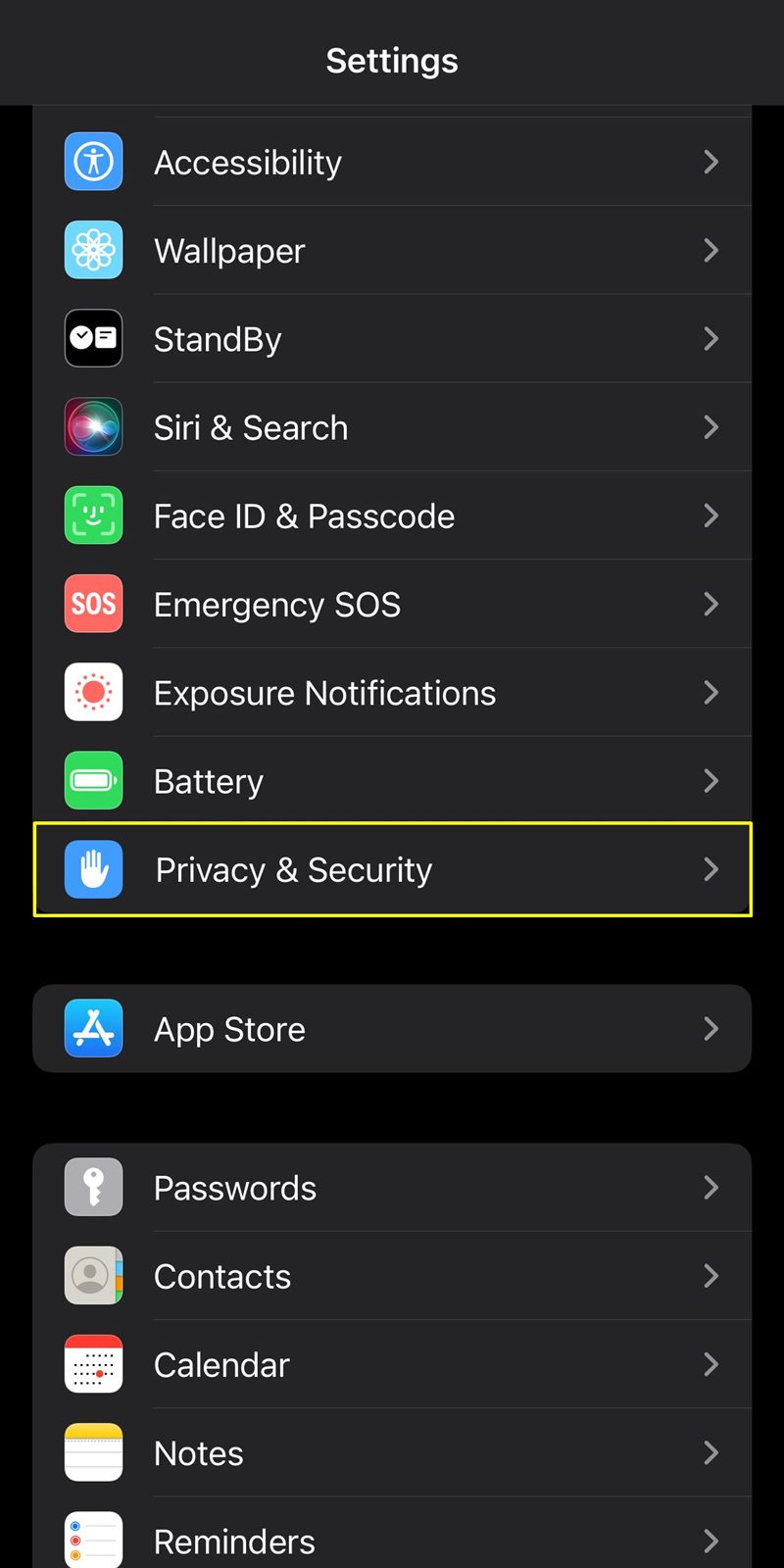
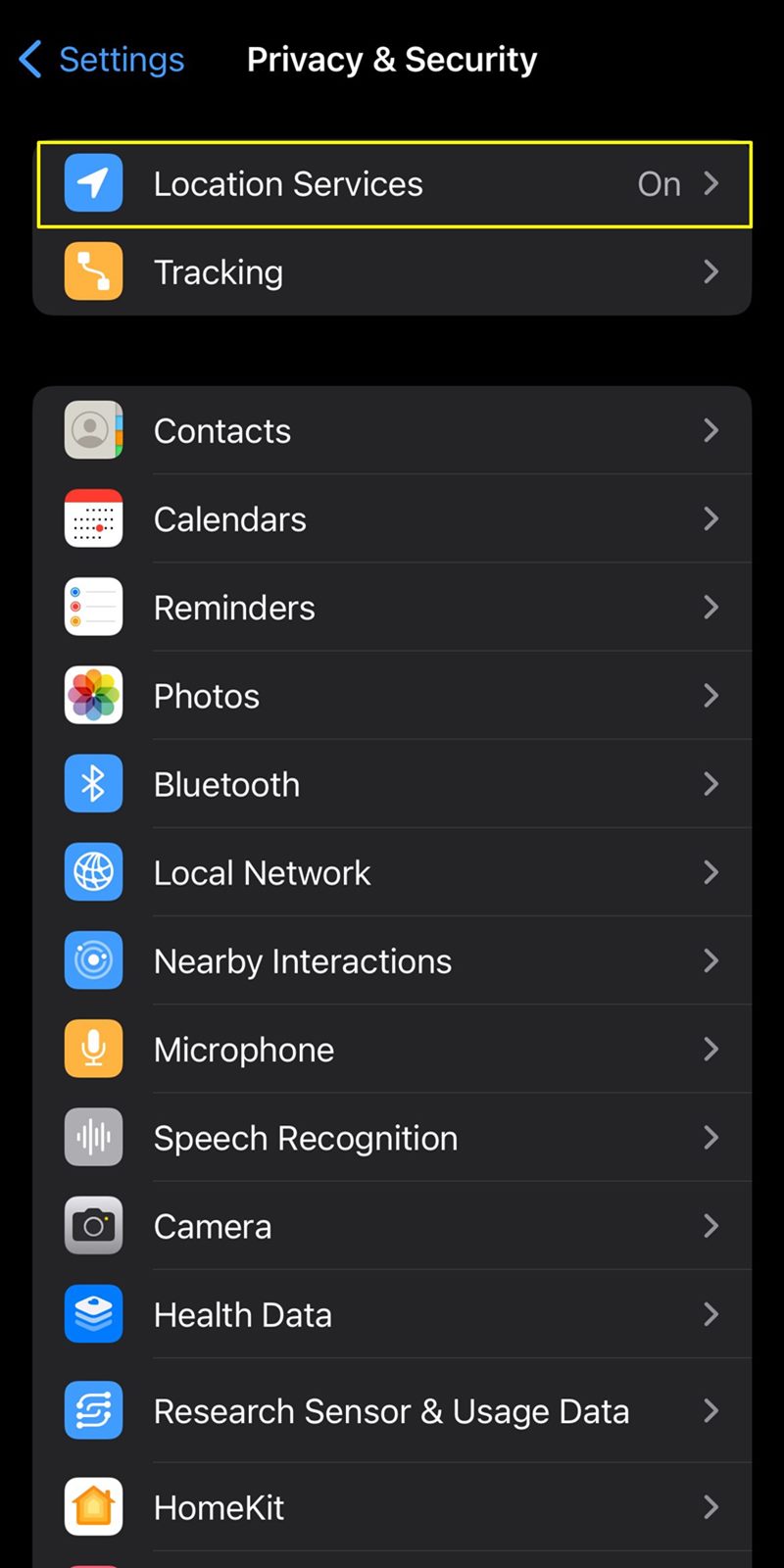
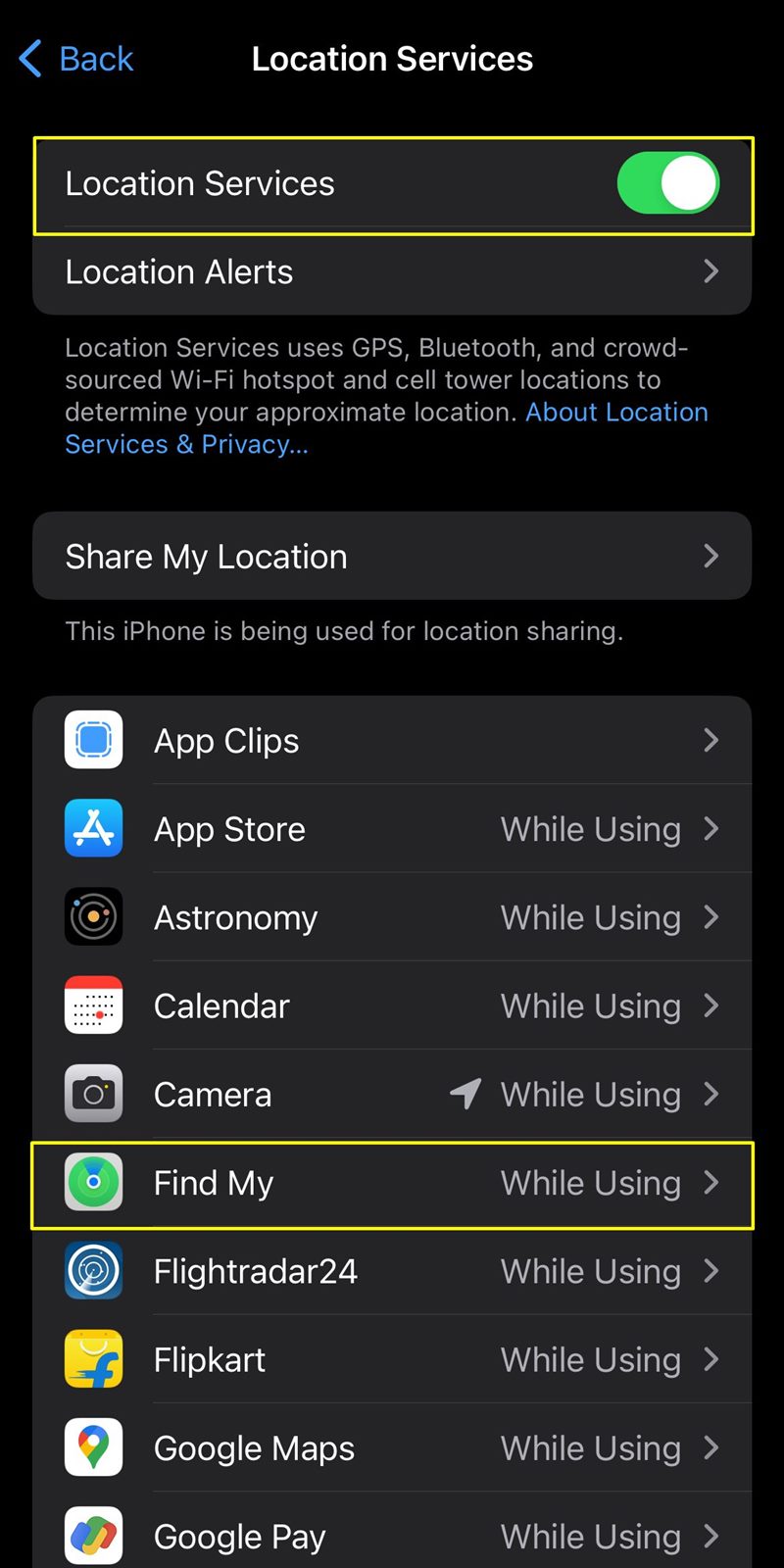
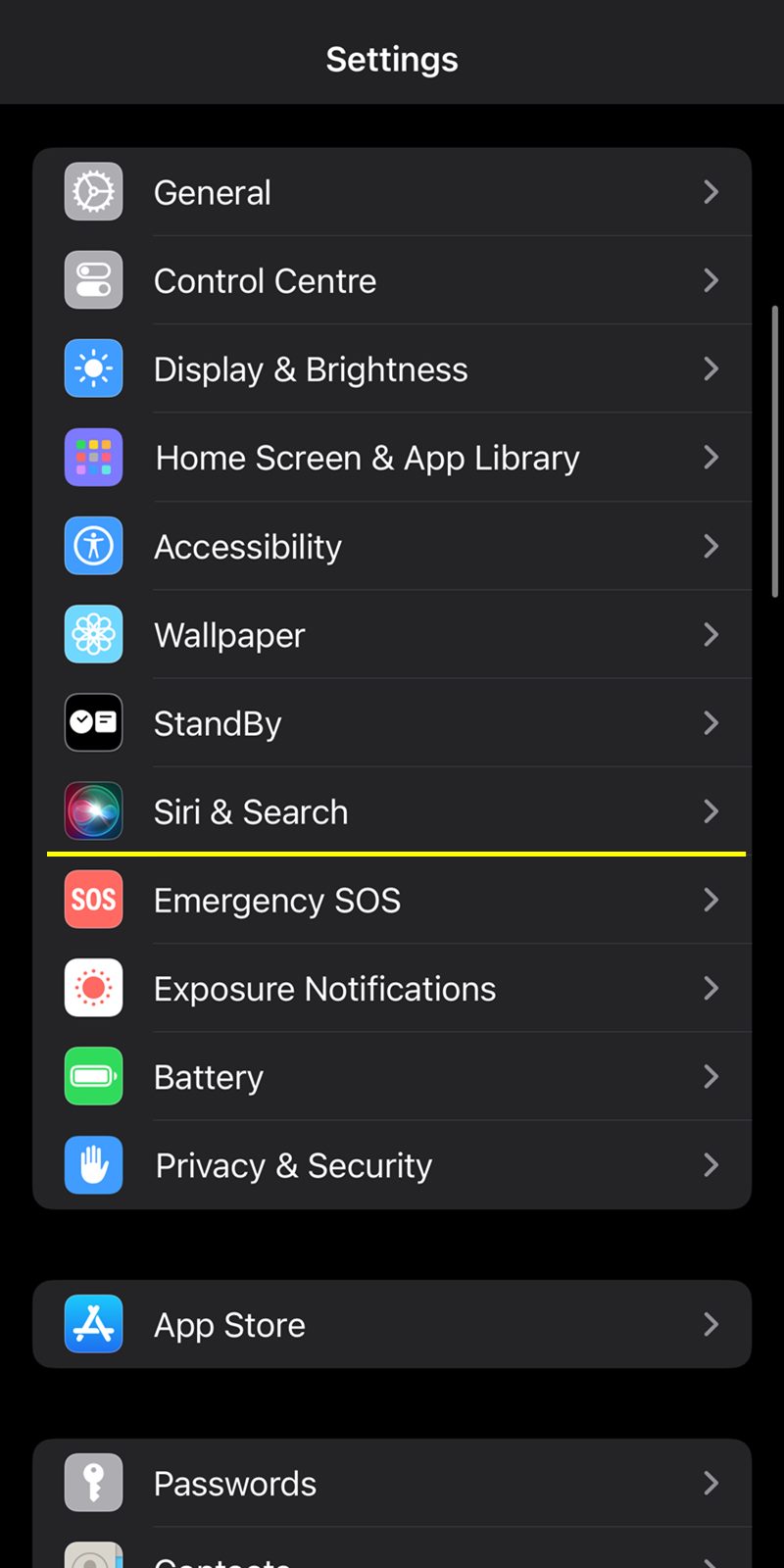
4. Activate "Location Services": Enhancing Security and Functionality
Enabling "Location Services" on your iPhone not only enhances the functionality of various apps but also plays a crucial role in securing your device. This feature aids in locating your device using GPS, which is particularly valuable in case of theft or misplacement.
Here is how to activate "Location Services":
- Open Settings.
- Scroll down and select "Privacy & Security."
- Tap on "Location Services" and toggle the switch to turn it on.
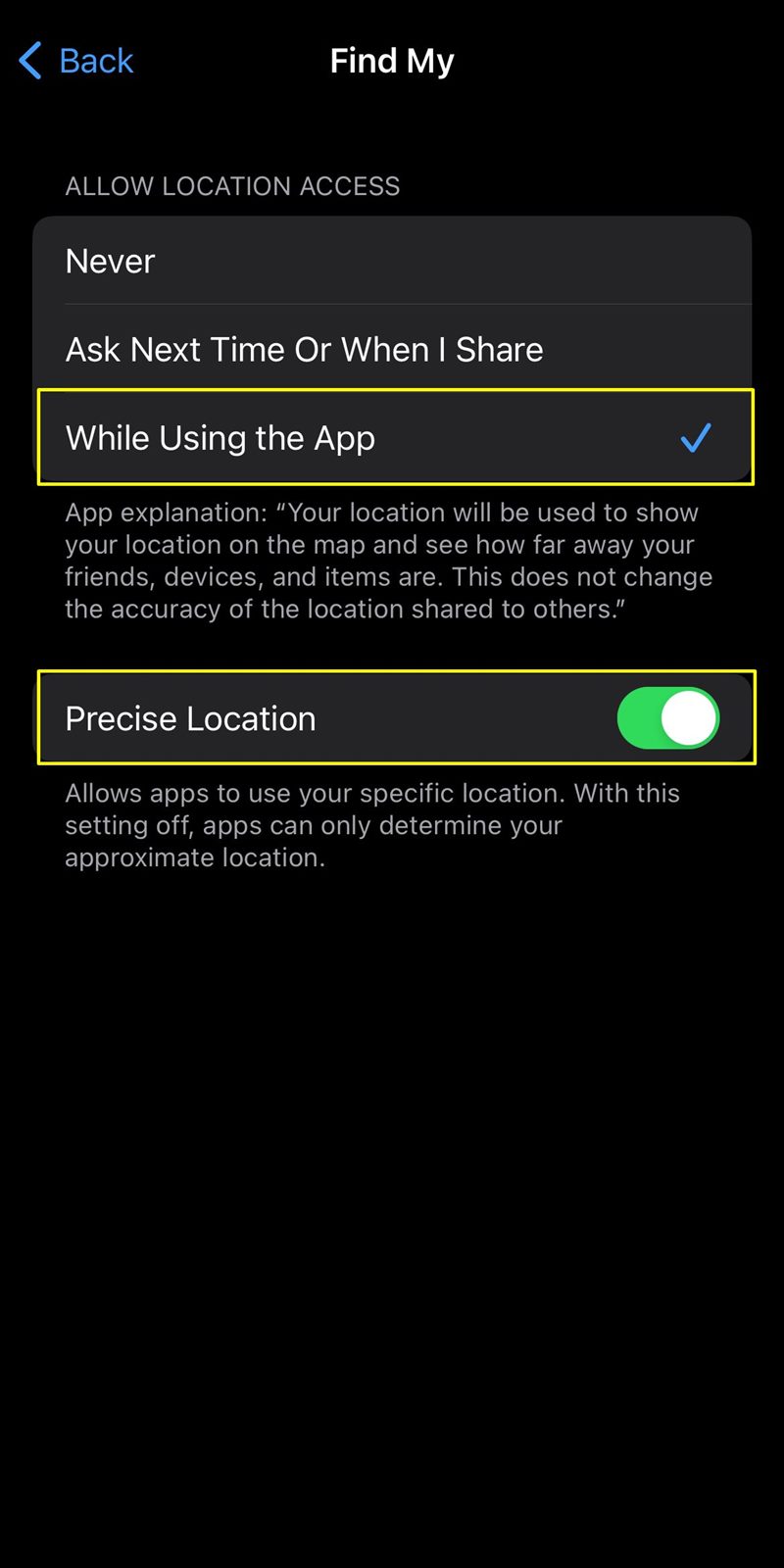
- Scroll down on the same page and select "Find My."
- Tap on "While Using the App" and toggle "Precise Location" as well.
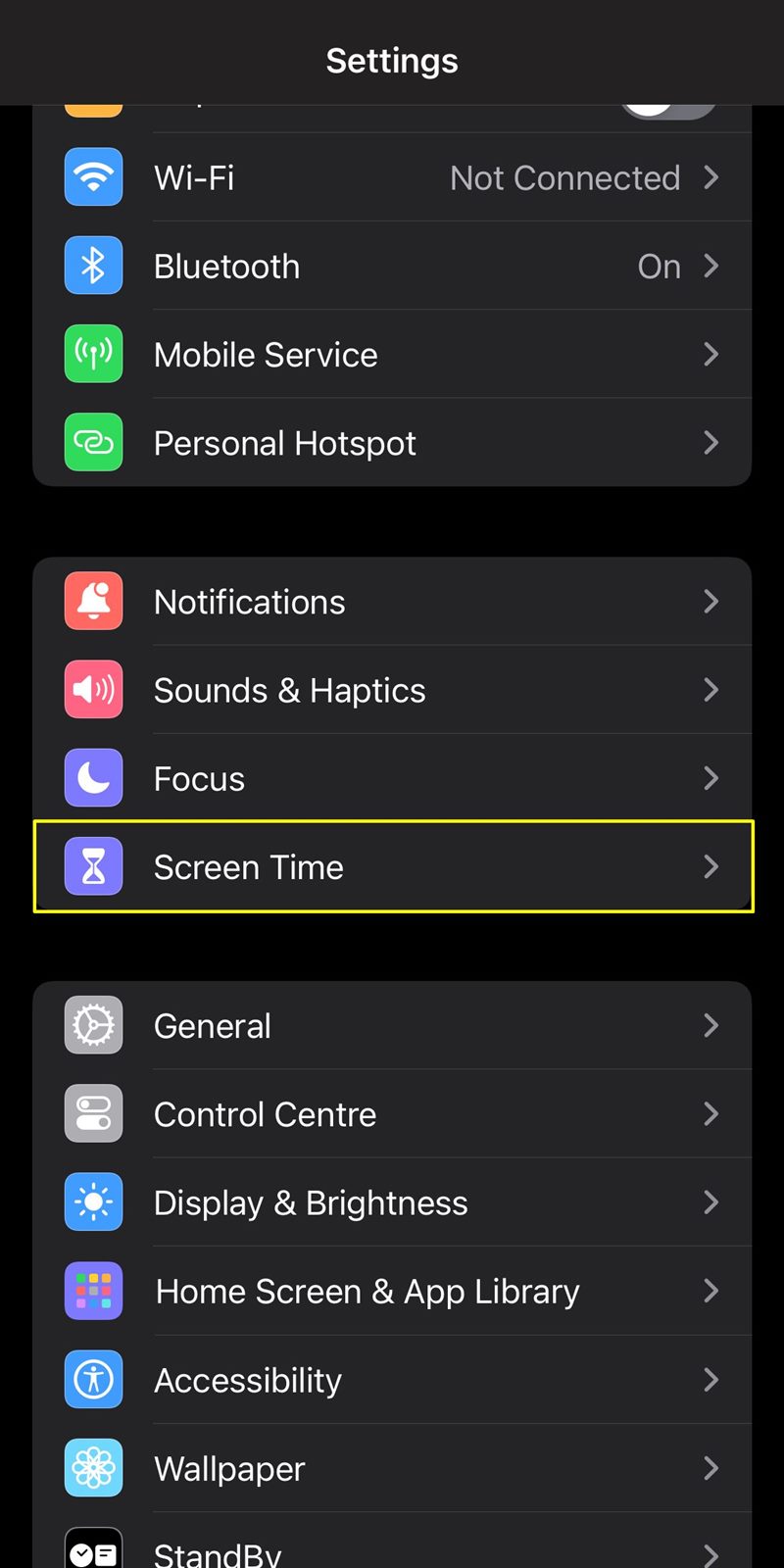
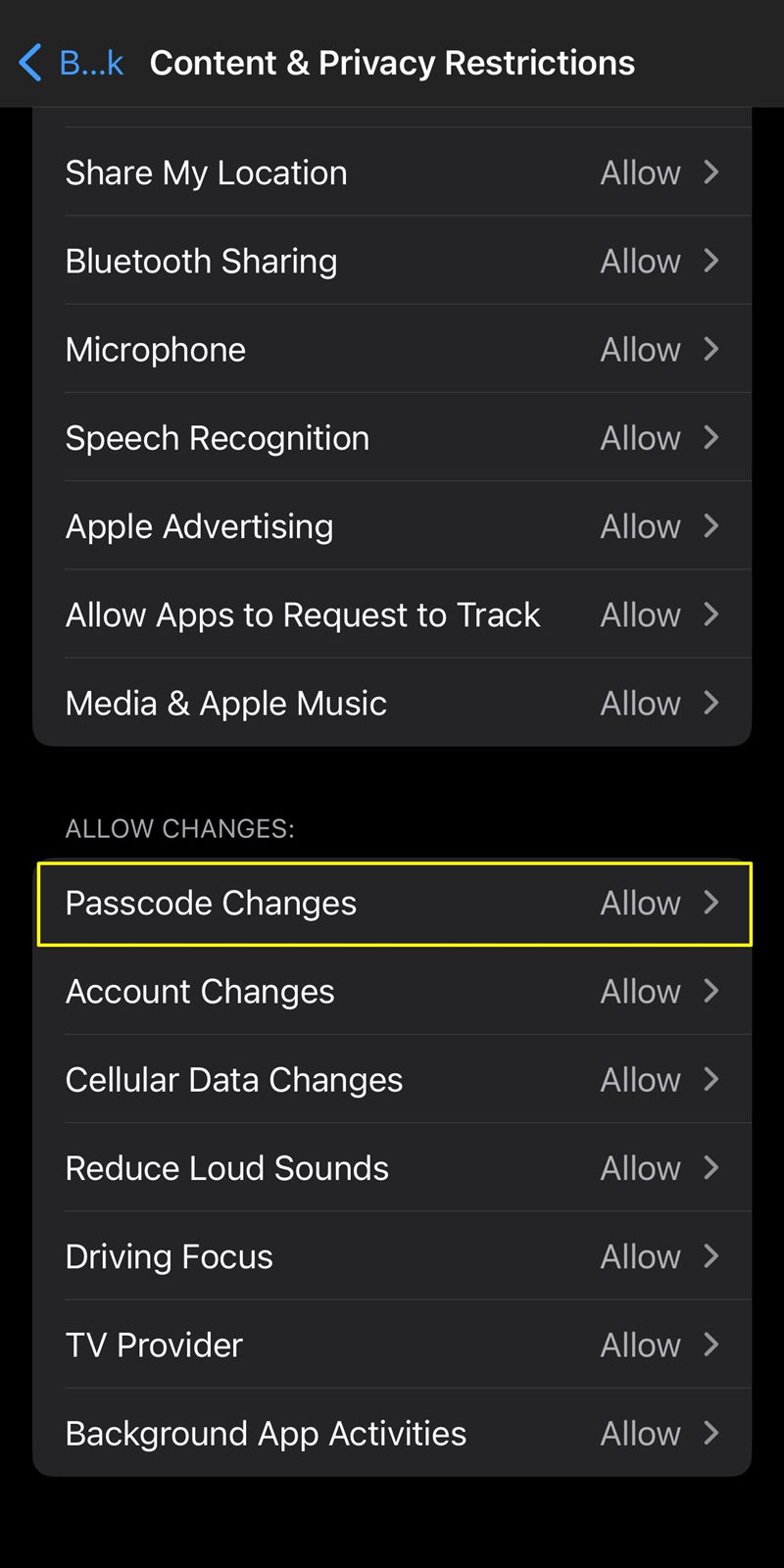
5. Strengthen Security with Content & Privacy Restrictions: Restrict Passcode Changes
Beyond the conventional security measures, utilizing Content & Privacy Restrictions provides an additional layer of control over certain aspects of your iPhone's functionality. One specific restriction worth implementing is preventing passcode changes without your authorization.
Here is how to disable passcode changes:
- Go to Settings.
- Tap on "Screen Time."
- Tap on "Content & Privacy Restrictions."
- Scroll down and select "Passcode Changes."
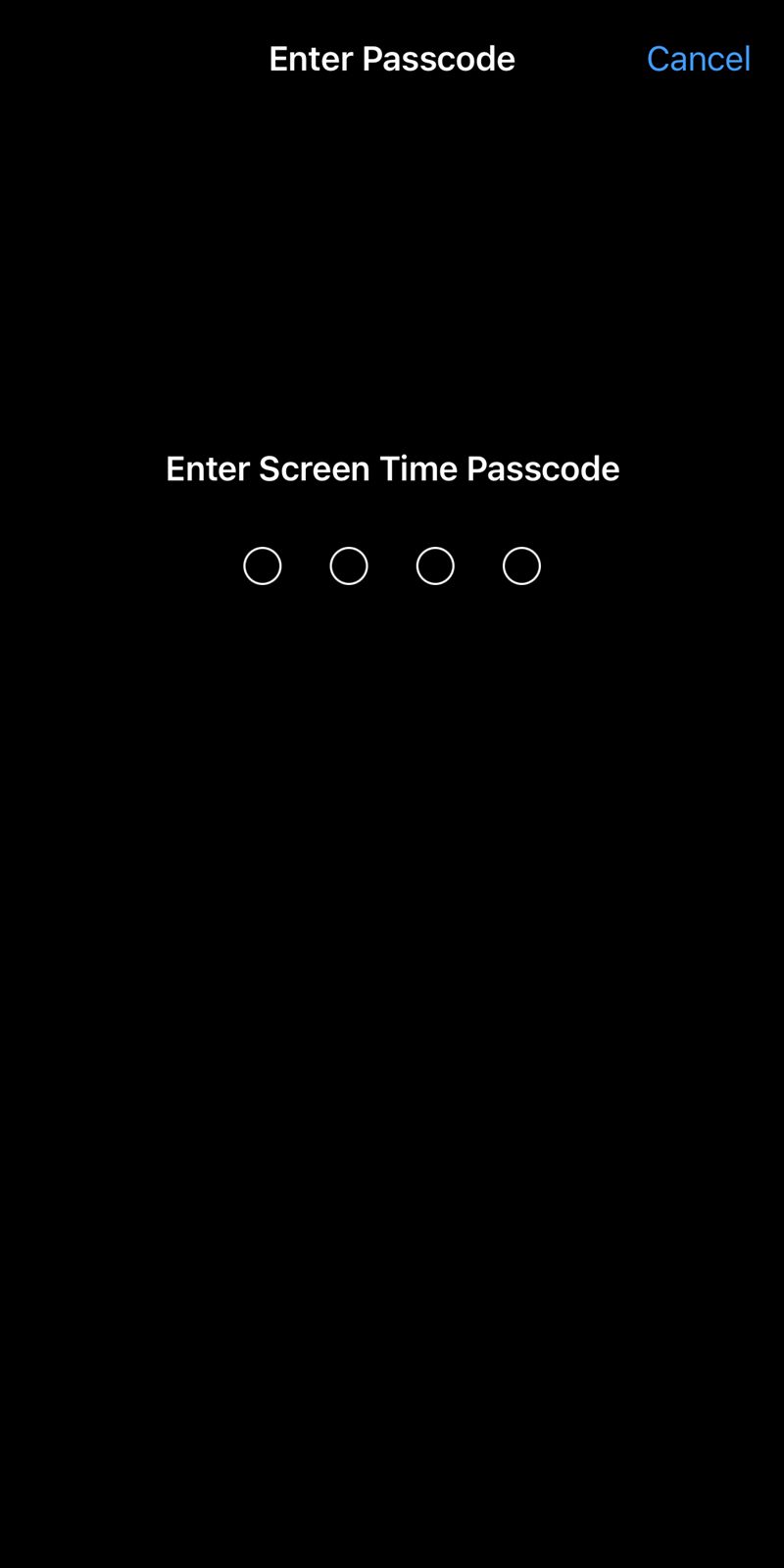
- Enter your passcode.
- Click on "Don't Allow."
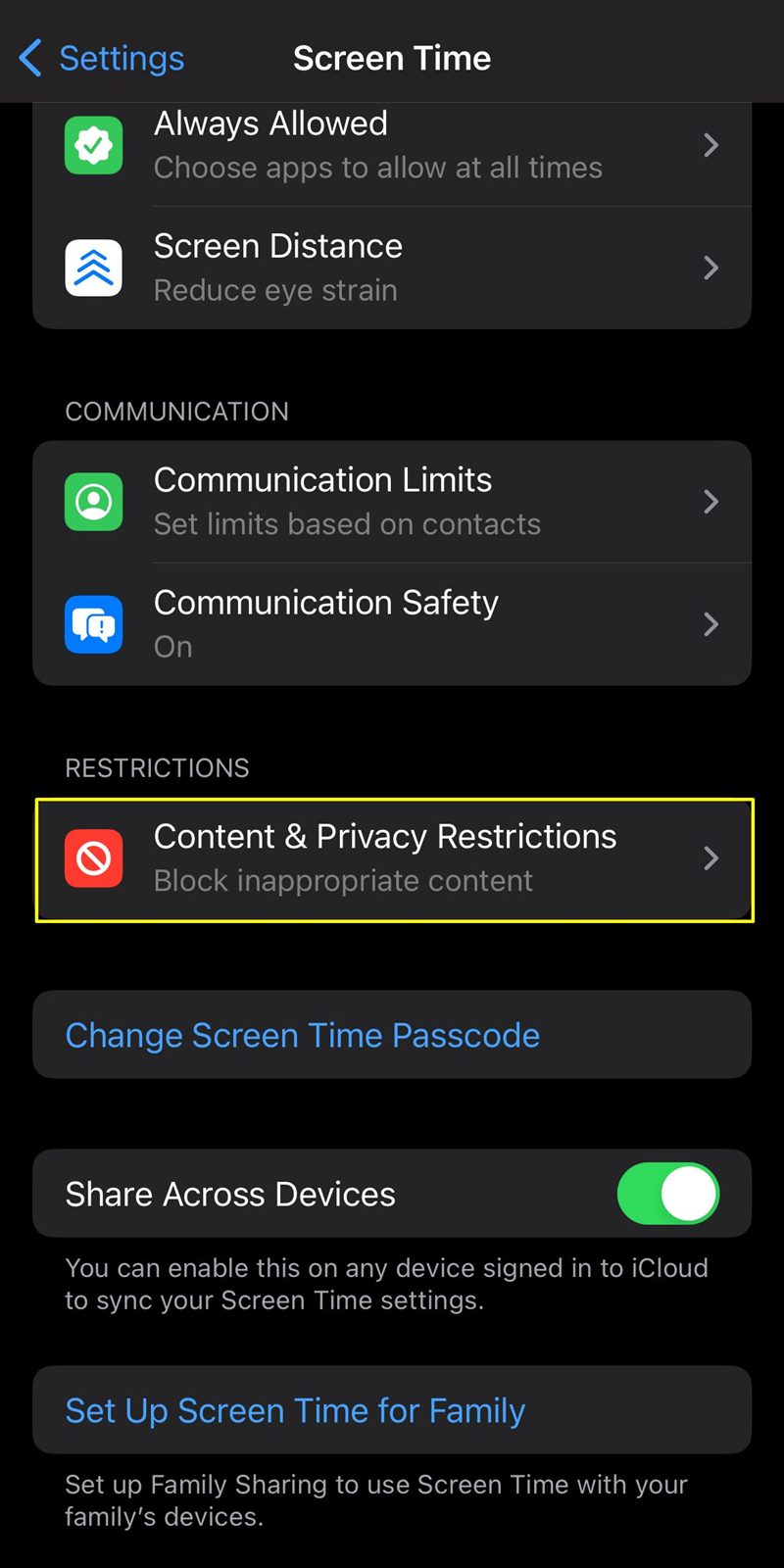
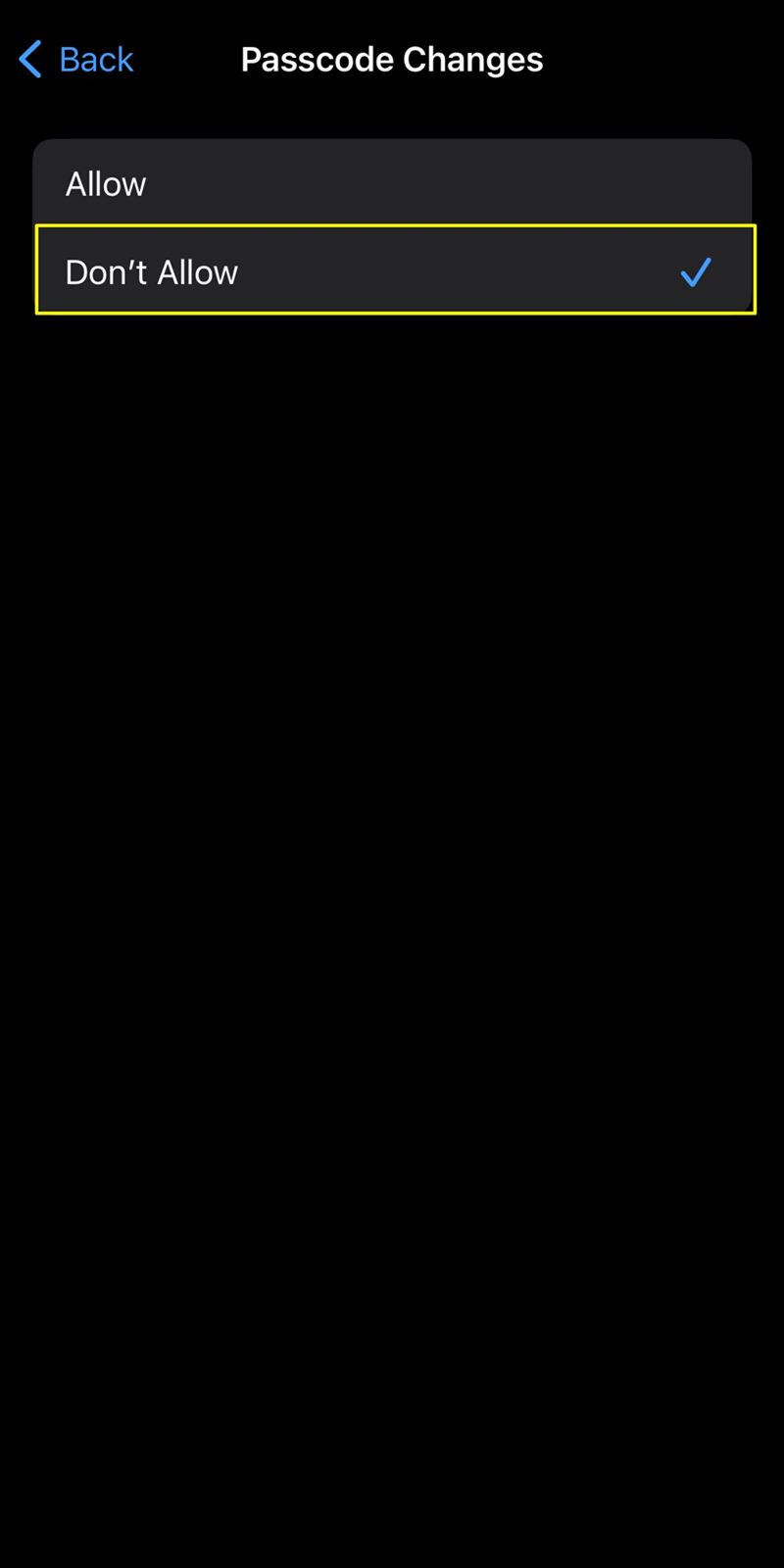
Important Consideration After Applying Content & Privacy Restrictions
It's crucial to be aware that implementing the "Content & Privacy Restrictions" and specifically setting "Passcode Changes" to "Don't Allow" has a direct impact on the "Face ID & Passcode" settings.
Once you restrict passcode changes, accessing "Face ID & Passcode" under Settings will be disabled. This is a deliberate security measure to prevent unauthorized modifications to your device's passcode, ensuring that the restrictions you've set remain intact.
If you ever need to adjust your Face ID or passcode settings after applying these restrictions, you will need to navigate back to "Content & Privacy Restrictions" under Screen Time. From there, you can manage the passcode changes and other security-related settings.
6. Enable Two-Factor Authentication (2FA): Double the Protection
Two-Factor Authentication adds an extra layer of security by requiring a verification code in addition to your password. This ensures that even if your password is compromised, unauthorized access is thwarted.
Here is how to enable Two-Factor Authentication:
- Go to Settings.
- Tap on your Apple ID.
- Select "Sign-In & Security."
- Choose "Two-Factor Authentication" and follow the prompts.
I have, however, already turned it on on my iPhone. If you don't, then follow the above steps.
7. Regularly Update Your iPhone: Stay Ahead of Vulnerabilities
Apple regularly releases software updates that include security patches. Ensure your iPhone's operating system, apps, and firmware are up-to-date to shield against potential exploits.
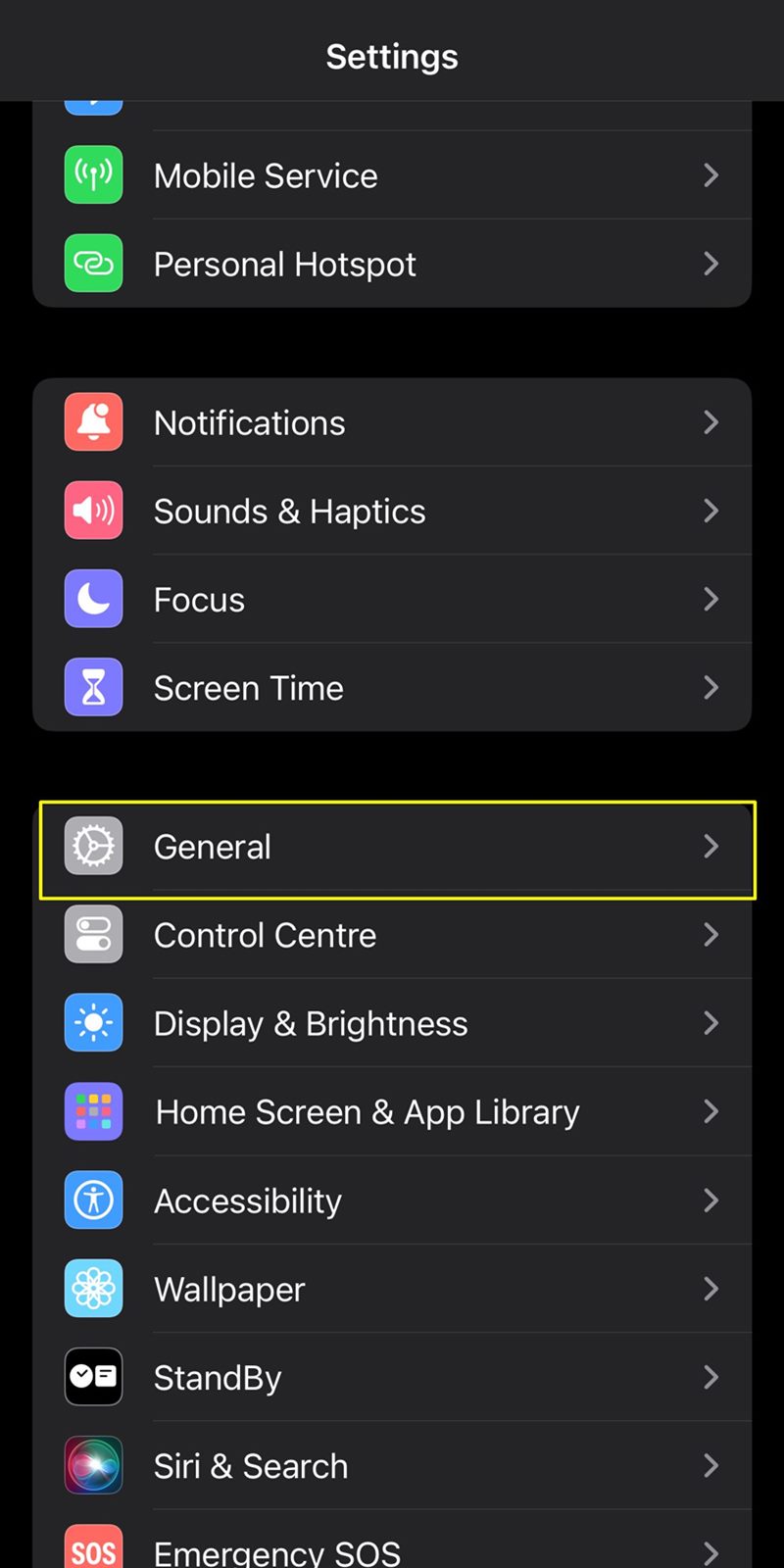
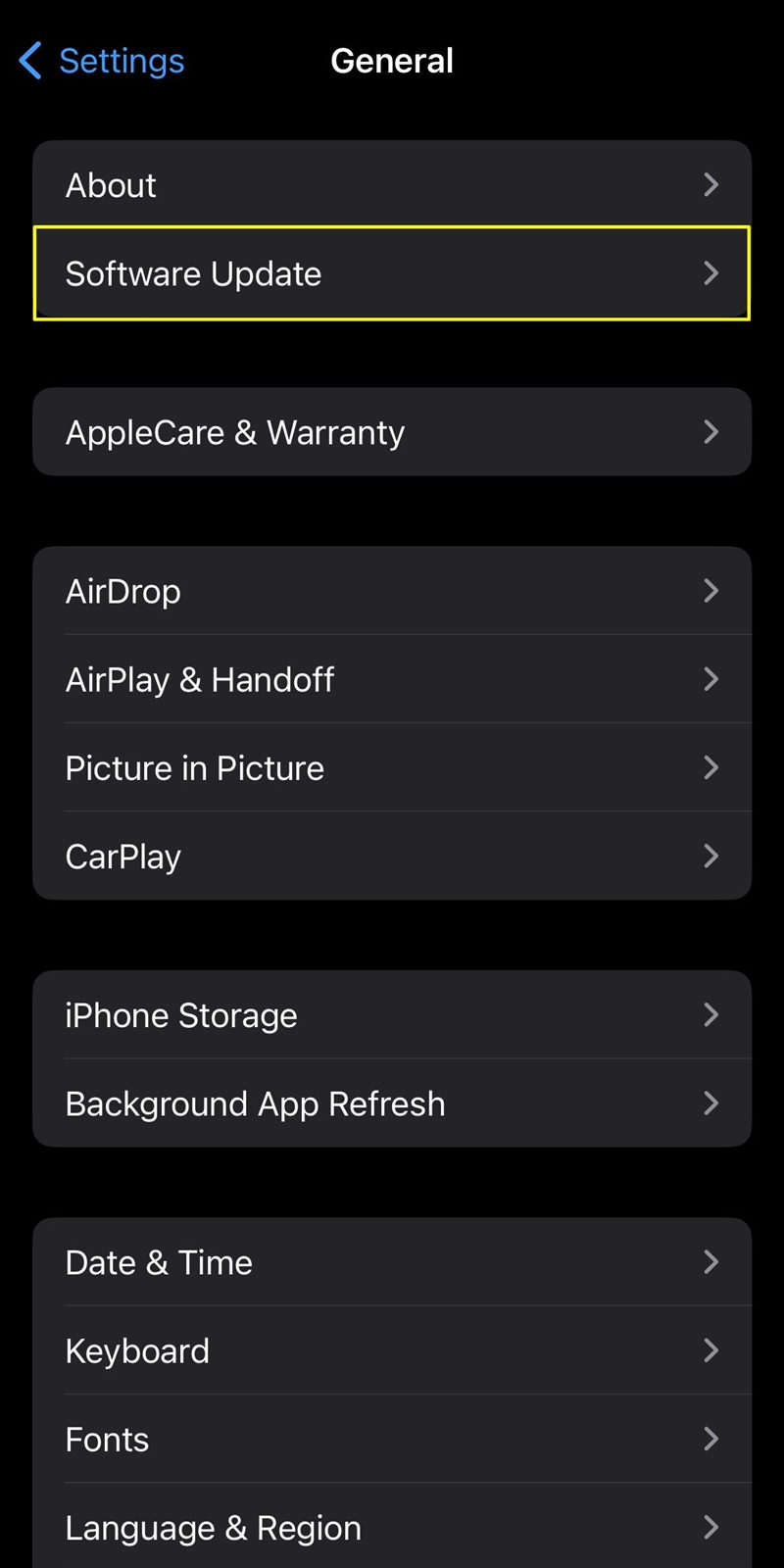
Here is how to update your iPhone:
- Go to Settings.
- Tap "General."
- Select "Software Update" and install any available updates.
8. Be Cautious with Third-Party Apps and Links: Avoid Potential Threats
Download apps only from the official App Store, and exercise caution when clicking on links, especially in messages or emails. Phishing attempts often target personal information.
9. Exercise Caution on Public Wi-Fi: Safeguarding Your iPhone from Potential Threats
Connecting to public Wi-Fi networks poses inherent risks to the security of your iPhone. These networks, often found in cafes, airports, and other public spaces, can be breeding grounds for cyber threats. To ensure your device remains secure while on the go, follow these guidelines:
- Avoid Automatic Connections: Disable the "Auto-Join" feature for public Wi-Fi networks to prevent your iPhone from connecting automatically. This gives you more control over the networks you join. To disable the "Auto-Join" feature for public Wi-Fi networks on your iPhone, go to "Settings" > "Wi-Fi" > "Ask to Join Networks" >" turn it off or select "Ask."
- Disable Sharing: Turn off sharing options such as AirDrop and file sharing when connected to public Wi-Fi. This minimizes the risk of unauthorized access to your device. Go to "Settings" > "General" > "AirDrop" >" select "Receiving Off" or "Contacts Only."
- Forget Untrusted Networks: Regularly review the list of saved Wi-Fi networks on your iPhone. Forget or delete any networks you no longer use or those that are unsecured and potentially risky. Go to "Settings" > "Wi-Fi" > "Edit" > "-" > "Delete."
- Verify Network Authenticity: Confirm the legitimacy of the public Wi-Fi network with the establishment's staff or use official signage. Avoid connecting to networks with generic or suspicious names.
- Enable HTTPS for Web Browsing: In Safari settings, ensure "Prevent Cross-Site Tracking" and "Block All Cookies" are turned on. Additionally, use websites with "HTTPS" in the URL for secure data transmission. Go to "Settings" > "Safari" >" and then toggle on "Prevent Cross-Site Tracking," "Block Pop-ups," and "Fraudulent Website Warning."
Disable Wi-Fi when you're not actively using it. This prevents your device from automatically connecting to available networks and reduces exposure to potential threats.
10. Strengthening Security with eSIM Technology
The integration of eSIM technology not only enhances connectivity but also contributes significantly to the security of your iPhone, especially in theft scenarios. Here's how eSIM can bolster the security of your device:
- Theft Deterrence: In traditional SIM card scenarios, a thief could easily remove the physical SIM card to prevent tracking. With eSIM, the embedded nature of the technology makes it significantly more challenging for a thief to disable connectivity.
- Remote Deactivation: In the unfortunate event of theft, you can remotely deactivate the eSIM through your carrier. This action renders the stolen iPhone useless for the thief, as it prevents any cellular communication on the device.
- Find My iPhone and eSIM: The combination of eSIM technology and the "Find My iPhone" feature creates a powerful synergy. Even if a thief manages to disconnect the device from Wi-Fi, the eSIM can still facilitate tracking and remote actions through cellular networks.
- Secure Device Wipe: With eSIM, the remote wipe feature becomes even more secure. In case of theft, you can initiate a secure wipe of your device's data, preventing unauthorized access to your personal information.
- Carrier Authentication: eSIM activation often involves a secure authentication process with your carrier. This authentication adds an extra layer of protection, making it more challenging for unauthorized users to tamper with or change your device's connectivity settings.
- Emergency Calls and Location: Even without a traditional SIM card, eSIM enables emergency calls and location tracking. This ensures that, in urgent situations, your device can still be located and used for emergency communication.
By incorporating eSIM technology into your security strategy, you not only fortify your iPhone against theft but also empower yourself with advanced remote control features. This added layer of security makes it significantly more challenging for thieves to compromise your device and helps ensure the safety of your personal information.
Conclusion: Strengthening Your iPhone's Defenses
By implementing these effective tips, you significantly enhance the security of your iPhone, protecting it against potential theft and unauthorized access.
Safeguarding your device is not just about the physical hardware; it's about securing the wealth of personal data it holds. Stay vigilant, stay updated, and take proactive measures to ensure your iPhone remains a fortress of security in an increasingly connected world.
Sharing is stylish! Gift your friends this awesome read!